Warning!!! The geocache is not at the posted coordinates!!! Do not look there!!!
Read below to learn how to solve a puzzle and find the actual geocache coordinates.
Good Luck
Puzzle caches take a lot of time to create and maintain, so if you would like me to continue placing quality caches, please don't leave generic logs like "TFTC" or "I found it at 12:00". Logs like this are rude to the cache owner and show a lack of appreciation. Thanks
퍼즐 캐시는 만들고 유지하는 데 많은 시간을 필요로하기 때문에 계속해서 고품질 캐시를 배치하려면 "TFTC"또는 "12:00에 찾았습니다"와 같은 일반 로그를 남기지 마십시오. 이와 같은 로그는 캐시 소유자에게 무례하고 감사의 부족을 보여줍니다. 감사합니다
Hello Geocachers! There are many of us out there who are addicted to the thrill of geocaching, and there are many types of geocaches. I don't know about you, but whenever I find a great geocache I get excited that I was able to figure out where it was hidden. However, with puzzle caches I get to experience that thrill twice, once when I solve the puzzle and then again after I find it.
After setting up many puzzle caches in Korea I have noticed that there are quite a few geocachers who actively avoid finding puzzle caches. Perhaps it is because the puzzle seems difficult, is a tedious extra step to excitement, or just don't know where to start. I want everyone to experience the joy of finding puzzle caches so I have set out to create a new series of easy puzzle caches designed to teach you how to become a puzzle master.
There are many kinds of ciphers that are used on geocaches. This puzzle is designed to help you know how to recognize and solve several of the most common types of ciphers used in geocaches.
Caesar cipher (ROT13)
The Caesar cipher or shift cipher method uses a simple substitution encryption. This means that every character is substituted by another character according to a specific system. The substitution character is determined by rotating the alphabet. For example, the well known and mostly used ROT13 method shifts the alphabet with 13 positions, this results in: A=>N, B=>O, ...,Y=>L and Z=>M. Every other shift is also possible. In the exceptional case of the ROT13 method with 13 rotations the same key can be used for encryption and decryption. This does not work for the other shifts, keep this in mind. This is also the cipher used by the Geocaching website when displaying hints.
A variation to the standard Caesar cipher uses a key word or alphabet key to alter the alphabet. The characters of the key word are added to the beginning of the substitution alphabet and removed from their original location. Needles to say, every character is still used only once in the alphabet, although they may be used more than once in the key word.
For example we can easily decode the following sequence using online tools like this Caesar Cipher tool which displays all possibilities at the same time. Give it a try
Gss kogb'h hvoh sogm! W ybsk mci qcizr rc wh!
Vanity code
The numbers in the vanity code correspond to letters using the phones number pad. The 1 and 0 do not correspond to any letter and will often be used as spaces. The numbers 2, 3, 4, 5, 6 and 8 are connected to three letters and the 7 and 9 to four letters as shown in the image.
Try using the image below to decode this message: 8 44 2 8 1 9 2 7777 1 33 2 7777 999 1 9 2 7777 66 0 8 1 444 8 0

Rail Fence cipher
Rail Fence Cipher (also called a zigzag cipher) generally refers to a form of transposition cipher. In the rail fence cipher, the plain-text is written downwards and diagonally on successive "rails" of an imaginary fence, then moving up when we reach the bottom rail. When we reach the top rail, the message is written downwards again until the whole plain-text is written out. The message is then read off in rows.
If you see a jumble of letters and spaces that looks like it could contain the words North or East, try using an online tool like this Rail Fence decoder to examine it.
Tel eshiphr latpsts r te n ueam mruehucel s szr ayaazla ihieoetizeen ztpknhl
After examining examination you can start to see a pattern emerge that decodes the message like this.

Bifid cipher
The bifid cipher is one of the classical ciphers and was invented around 1901 by Felix Delastelle. Bifid is a combination of substitution and fractionization, this causes the original text to spread over the entire encryption, which is more secure. It does this by using something called a Polybius Square and then filling in the boxes with letters of the alphabet. As there are only 25 boxes I, J, or Q are often substituted out of the cipher. Furthermore, to add an extra layer of encryption a keyword can be used to mix up the letters in the Polybius Square.
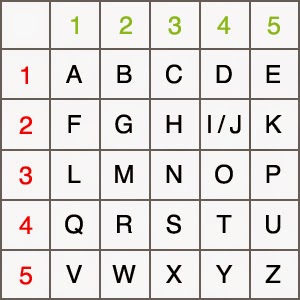
An excellent tool used for decoding the bifid cipher is HERE!
Puzzle
This is not a list of every cipher used on geocaching puzzles, just a few of the most common and simple ones.
Now that you have seen a few different ciphers, how about trying to solve one on your own? Good Luck!
20 19 25 22 20 1 22 15 22 25 25 15 7 24 20 16 15 2 25 3 25 2 25 22 16 15 16 20 1 3 15 10 25 15 7 24 20 25 15 7 24 20 25 15 7 24 20

You can validate your puzzle solution with certitude.