There is nothing hidden at the listed coordinates: solve the puzzle to get the location of the cache.
The dedication, innovation and brilliance of the men and women who worked at Bletchley Park and its equivalents elsewhere defy comparison. This series of cryptographic puzzles exists to celebrate their achievements, and to challenge those capable of visiting their arcane world.
| Please be aware that these are rather specialised and extremely difficult puzzles. I set out to create something worthy of the B.P. cryptographers themselves, and that inevitably puts the series beyond the reach of many people. The messages are all in English and you won’t need to be a mathematician to solve the puzzles (I’m not) but you must be able to think like one - and to be prepared to research, learn and experiment. Be aware that each puzzle took me several weeks of research and investigation to construct and validate; so solving them will be a lengthy process. But I promise that they are all entirely doable. |
| I appreciate that whilst Joan and her colleagues were quite accustomed to solving quite complex problems within nothing more than a sharp pencil, a pad of squared paper and a really strong cup of tea, latter-day solvers may have grown a little soft. Consequently I make available here a few modular matrix algebra tools that might come in handy. |
The following week they had another lucky break. Somehow (she had her suspicions) Major Tester had managed to get his hands on a partial crib for one of Monday's messages. That had got them into the day's traffic and given them the feedback settings for the week. But once the start position changed the following day they were back to square one. There were suspicions that the enemy was paying more attention to COMSEC.
She was getting nowhere. Time to work on something else. She sent the file back to registry and turned to other matters.
An hour or so later she found herself thinking about FINBACK again. She sketched out the shift register connections for the week's feedback function.
Tantalising, but not much use without knowing the initial register state. What she needed was a crib: some sort of predictable content in a message... or maybe across several messages. Hmmmm... there were just a few bits that she might be able to use to get a toe-hold.
Fetching the file again, she picked out a promising message
TX BEGINS 08:28:50Z
00010 10111 11100 01110 00110 11100 00010 11111 01000 10010 01001 01100 10011 10111 01111 11100 11000 10010 01001 11011 10101 00000 10100 01001 00101 01111 10111 11101 11110 11000 01100 00011 10000 11000 11110 01101 11001 00011 11011 11100 00110 00000 11000 11110 00100 10001 01011 11101 00011 10110 01000 11111 01011 11010 01110 10111 01010 11101 11101 00010 01010 01010 00000 11001 00011 10100 10010 00110 01001 10000 10101 01101 10000 11011 11100 11001 11000 11010 11101 11110 01011 00010 00111 11001 11110 11000 01110 10000 10100 01000 11100 11100 01011 10101 00111 10000 00011 10110 00001 10000 11110 10110 11010 01100 01000 10011 01110 10000 10001 00000 01100 01000 00111 11000 01110 01000 01100 00000 00010 01000 11111 00101 01010 00100 10110 00110 00001 00101 00001 00001 11001 00101 10010 11111 11000 11001 01110 11010 01100 11000 01011 10110
TX ENDS 08:29:03Z |
Call that message 1. Now... counting carefully, she tabulated the lengths of this and the following transmissions, and their initial cypher bits :
| message 1 |
142 chars |
begins 00010 |
| message 2 |
227 chars |
begins 00110 |
| message 3 |
239 chars |
begins 01100 |
| message 4 |
217 chars |
begins 00010 |
| message 5 |
233 chars |
begins 11101 |
| message 6 |
248 chars |
begins 01110 |
| message 7 |
202 chars |
begins 00010 |
| message 8 |
101 chars |
begins 00000 |
| message 9 |
275 chars |
begins 00010 |
| message 10 |
264 chars |
begins 10001 |
| message 11 |
158 chars |
begins 00010 |
| message 12 |
163 chars |
begins 10001 |
| message 13 |
145 chars |
begins 01100 |
Right. She had an approach in mind but she was going to need some help to make it work.
Time to talk to Major Tester.
Background Briefing
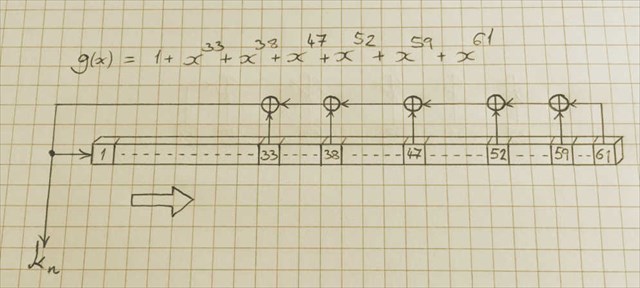
The enemy is known to be using a Vernam cypher with a key stream generated by a 61 bit linear feedback shift register. The underlying plaintext is 5 bit teleprinter (ITA2) code transmitted LSB (impulse 1) first. |
Many congratulations to Lilla22 on the FTF